Our Products
Software solutions to help your business achieve achieve it’s Identity Management and Security goals
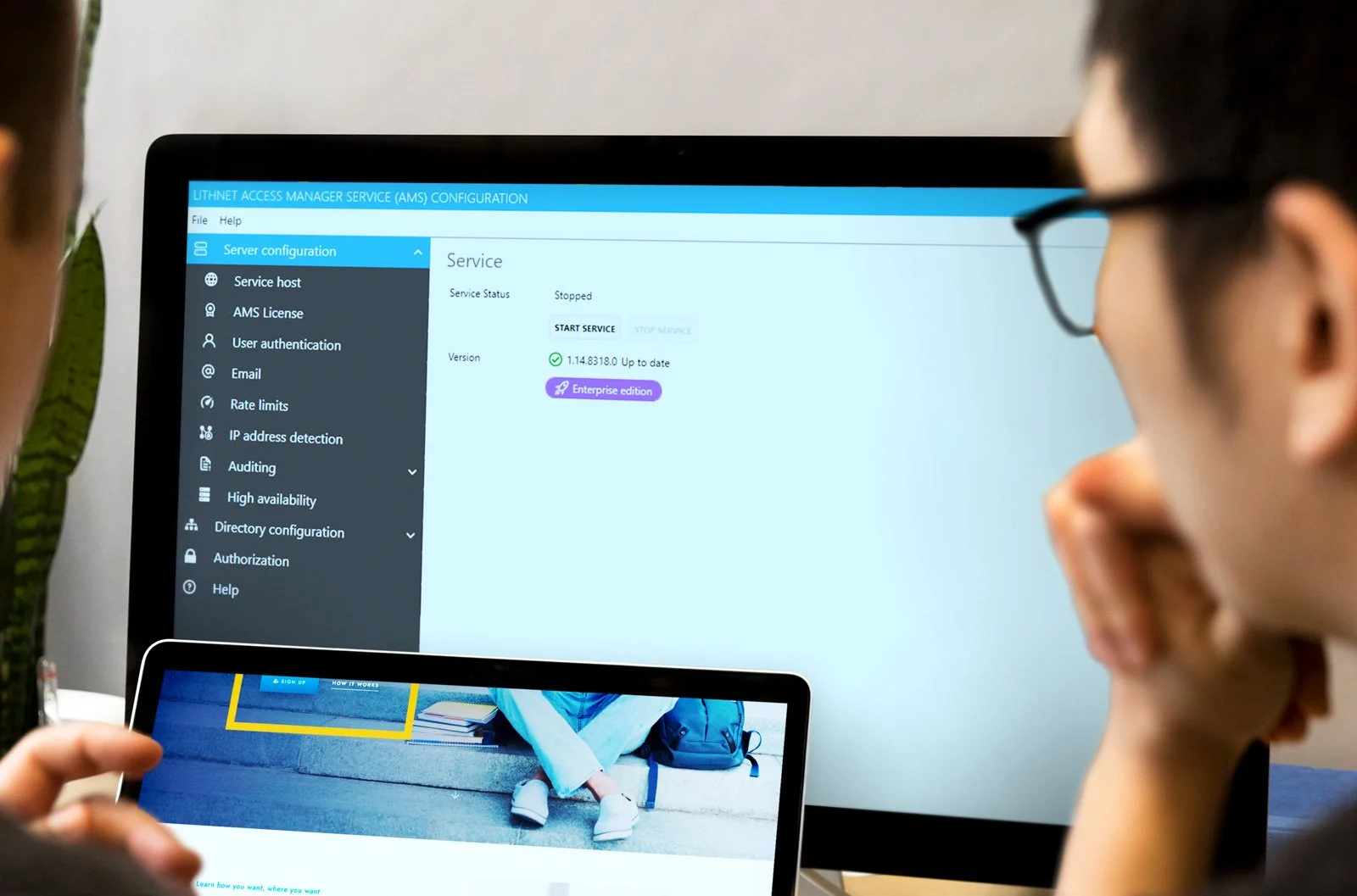
Lithnet Access Manager
A software solution that allows you to safely delegate sensitive administrative access to computers within your organization in a modern and user-friendly way.
Access Manager provides a web-based interface that allows users to request local admin/root passwords, BitLocker recovery keys and grant just-in-time administrative access to their own accounts. And with the product’s most recent update, it now features RapidLAPS—a passwordless LAPS experience, and offers passphrases as an option for passwords.
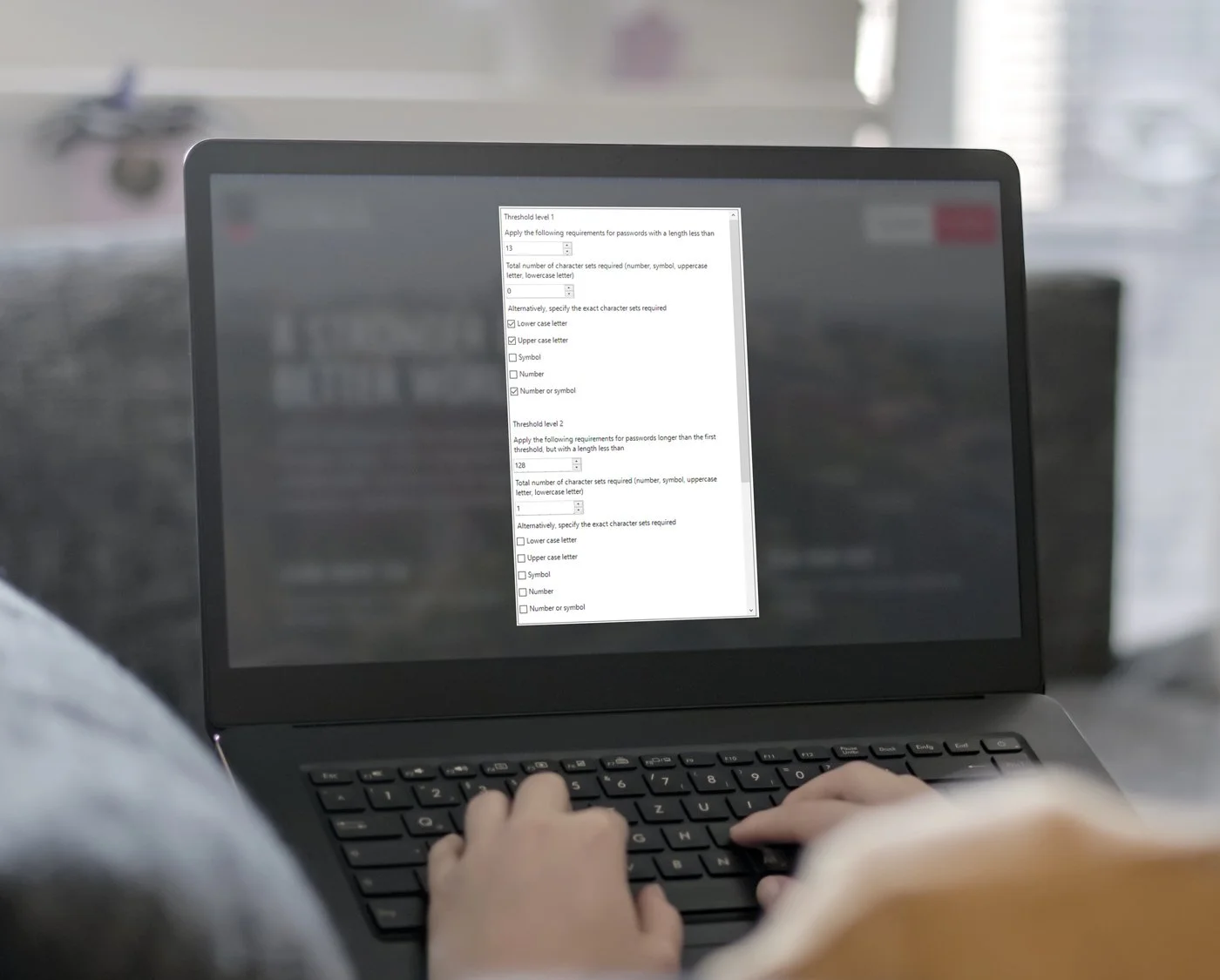
Lithnet Password Protection for Active Directory
A module for Active Directory that uses a password filter to inspect passwords as users attempt to change them.
Using group policy, you customize the types of checks you want to perform on those passwords and they are either rejected or approved, and committed to the directory.
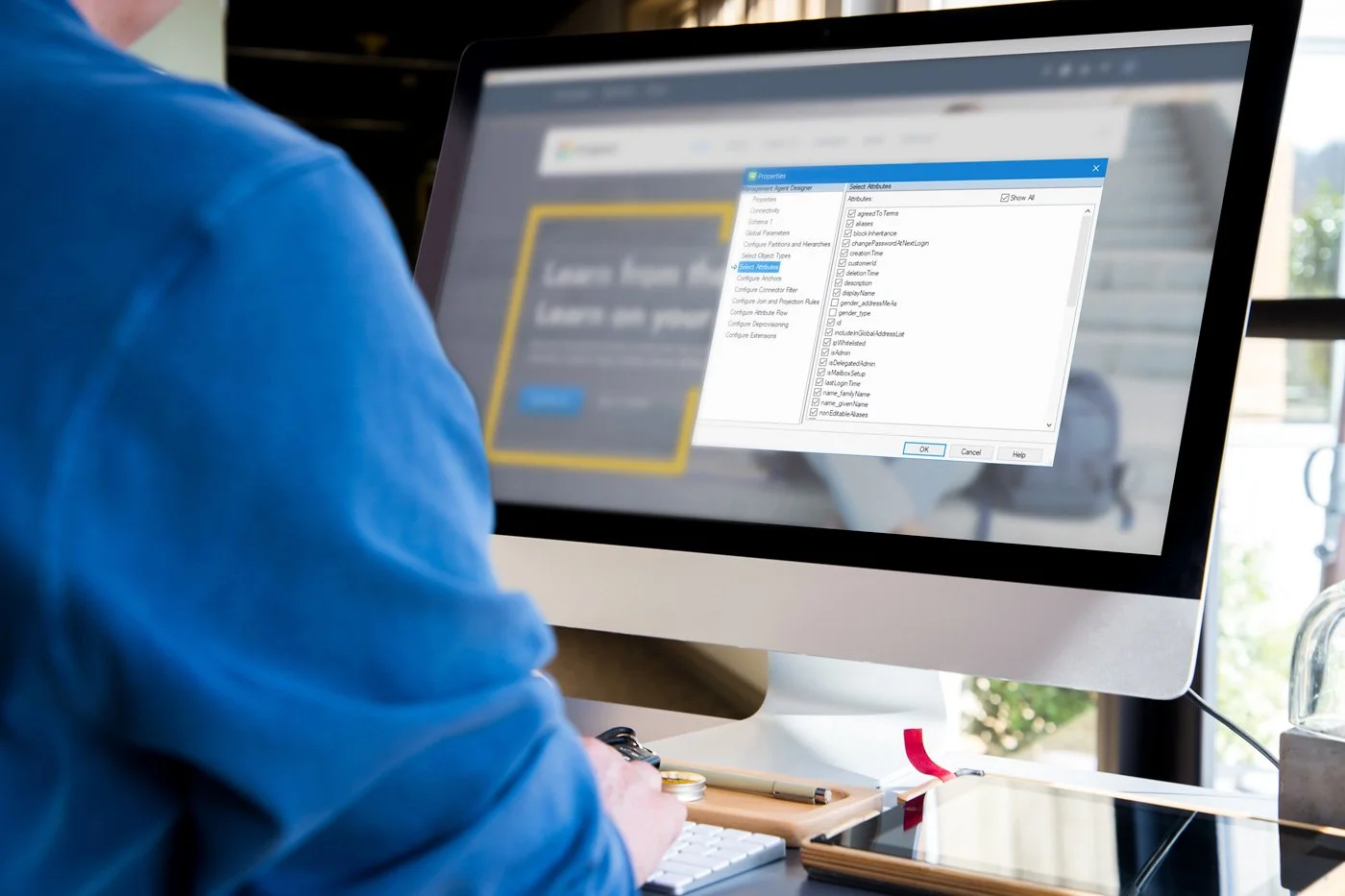
Microsoft Identity Management Toolkit
Extend the functionality of your MIM environment with our tools, PowerShell modules, and custom management agents for Microsoft Identity Manager.

Documentation
We know transparency saves operational time and increases success. Get the full picture of our products by accessing our documentation below.